Казино Vegas Grand — Для начала игры на официальном сайте — необзодимо пройти процесс регистрации. Для входа на сайт можно использовать рабочее зеркало www.vegas-grand63.com – официальные копии главного сайта. Отличительная его особенность перед множеством других подобных заведений — это наличие одного из самых обширных плейлистов с гаминаторами. Если на старте их было всего 120 штук, преимущественно от студии Microgaming, то сейчас слотов там более 2000.
Рабочее зеркало казино — это альтернативный веб-адрес, который ведет на официальный сайт казино, но при этом обходит блокировки и позволяет получить доступ к игровому контенту.
Содержание:
- Регистрация и вход
- Официальный сайт
- Рабочее зеркало
- Ввод и вывод средств
- Бонусы и привилегии
- Тех. поддержка
Подарки за регистрацию в Vegas Grand:
| Название | Пpиветственный 100% | Фриспины |
| Миндеп | 500 pyблей | 500 pyблей |
| Вейджеp | х30 | х30 |
Казино Vegas Grand регистрация и вход
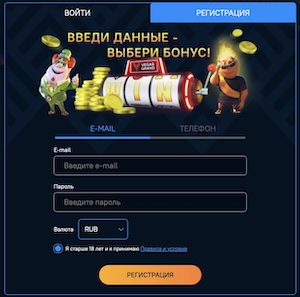
Регистрация в казино Vegas Grand специально упрощена, чтобы пользователи могли уже через 3 – 5 минут после входа на официальный сайт или любое зеркало начать играть на реальные деньги. От гемблера здесь нужны только номер телефона (или адрес электронной почты), а также пароль (можно указать любой, по собственному усмотрению). К некоторым гемблерам могут применяться требования о прохождении верификации, для подтверждения личности. Это нужно в тех ситуациях, когда ежемесячно гемблер вывод по 10 – 20 тысяч долларов со своего персонального счета (или больше).
Верификация инициирована именно европейской гемблинг-комиссией, призвана обезопасить от незаконного отмывания денег.
Форма входа:
Личный кабинет — это место, где можно заполнить дополнительную контактную информацию (по желанию), а также указать номера банковских карт, электронных кошельков для пополнения счета и вывода выигрышных средств. Зайти в него на официальном сайте или рабочем зеркале легко. Достаточно войти в уже зарегистрированный аккаунт Казино Вегас Гранд, используя электронную почту и пароль или авторизацию через социальные сети. В личном кабинете помимо контактных данных есть еще история произведенных финансовых операций, транзакций, там же можно пополнить игровой счет или вывести средства, есть раздел бонусов и подарков, раздача которых часто происходит в группе ВК или на самом сайте. Обычно бонусы к ставкам приурочены к праздникам или шествиям. В личном кабинете их можно активировать, получив скидки, кэшбеки, бонусы на вывод и пополнение средств, увеличение выигрыша и другое. Там же есть специальные игры, которые вы лично пометили для себя «любимыми» для более удобного совершения ставок. В службу поддержки также можно обращаться через вкладку личного кабинета.
Официальный сайт
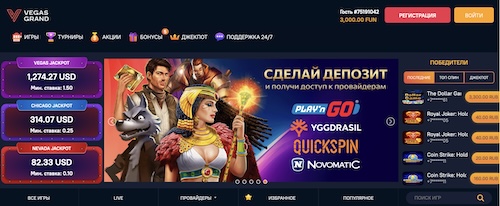
Всего официальный сайт Вегас Гранд переведен более чем на 3 языка. Это является лишь подтверждением, что играть там можно буквально с любой точки на планете. Вместе с этим игрок может выбрать любую удобную для себя валюту игрового счета. По умолчанию используются доллары. Но всего в казино Vegas Grand поддерживается свыше 10 валют, включая и российские рубли, и казахстанские тенге, и евро, и доллары. И конвертация производится автоматически. Причем, используется именно биржевой курс, который на порядок более выгодней банковского. Например, у пользователя банковская карта в рублях. Со своего депозита он выводит доллары. На счет будут зачислены именно рубли, но по выгодному курсу.
Ещё одна отличительная особенность: на официальном сайте вовсе отсутствует сторонняя реклама. Ни баннеры, ни предложения перейти в другой игорный клуб. На главной странице изредка публикуются только новости о новых добавленных играх, а также об запланированных на ближайшее время турнирах, что будут проведены на официальном сайте.
Рейтинг официального сайта:
| Название площадки | Рейтинг |
| Casinoglobal | 8 (из 10) |
| Casinotopsonline | 8 (из 10) |
| Trust | 7 (из 10) |
| Latestcasinobonuses | 6,6 (из 10) |
| Casinoking | 9,1 (из 10) |
| Kasino-narubli5 | 4 (из 5) |
| Topcasinoexpert | 7 (из 10) |
| Kazinohi | 3 (из 5) |
Рабочее зеркало на сегодня
Официальное зеркало онлайн казино — это полноценная копия официального ресурса. Этот дубликат позволяет в любое время зайти и поиграть в игровые автоматы. Рабочее зеркало размещено под другим доменным именем. Для входа на него потребуется специальная ссылка. Ссылки публикует официальный сайт Вегас Гранд, а также партнерские ресурсы и форумы.
Платформа-дубликат обеспечивает доступ к популярным играм в любое время в режиме 24/7 без выходных, обеденных перерывов и праздничных дней. Рабочее зеркало дублирует не только интерфейс и игровой каталог, но и набор программ, обеспечивающих безопасность и конфиденциальность. Пользователь может быть уверен в том, что его персональные данные и банковские реквизиты будут храниться в не меньшей безопасности, чем и на родительской платформе.
Рабочее зеркало Vegas Grand предоставляет ретро и прогрессивные слоты, настольные, мобильные игры. Для оплаты доступны удобные платежные методы. Рабочее зеркало позволит войти на сайт при блокировках, вызванных следующими ситуациями:
- атаки хакеров;
- запрет доступа РНК;
- блокировка провайдером сети;
- сбой на серверах казино;
- ухудшение метеорологических условий.
В любой перечисленной ситуации Vegas Grand предлагает найти рабочее зеркало по ссылке, которую можно получить у техподдержки, в рассылке, скопировать на основном ресурсе. Зеркало предоставят бесплатно. Оно абсолютно надежно и безопасно.
Сохраните несколько актуальных vip зеркал, чтобы не тратить время на поиски в будущем:
| go-vegas.ru | vegas-granda.ru |
| grandkip.ru | vegas-grand63.com |
| vegas-grand64.com | vegas-grand.com |
| VegasPlus.ru | grand22.ru |
| grand-e.ru | vegasgrandcasino-777.ru |
Ввод и вывод средств
Портал поддерживает 13 методов транзакций, постепенно интегрируются новые, что связано с желанием сделать переводы более удобными для клиентов и периодическими блокировками отдельных сервисов. По статистике гемблерам удобнее всего проводить взаиморасчеты посредством карт, но прямые платежи через многие банки ограничены. Поэтому пользователи ищут им альтернативы.
| Платежная система | Минимальный депозит |
| Банковские карты MasterCard, Visa, Maestro | 500RUB |
| Qiwi | 100 RUB |
| WebMoney | 350 WMR (350 RUB) |
| Bitcoin | 1000 RUB |
| SMS | Не более 5 сообщений в течение 5 минут |
| Мобильный платеж | 50 RUB |
Заявки на вывод обрабатывают в течении 24 часов, по факту намного быстрее.
Бонусы и Привилегии
После регистрации все новенькие клиенты игровой платформы получают свои первые бонусы. Официальный сайт Вегас Гранд казино предлагает новичкам бонусы на первые 5 пополнений игрового счета. В приветственные пакеты входят фриспины и бесплатные деньги. Сайт дарит подарки участникам ВИП-программы. Продвигаясь по уровням, игроки накапливают баллы и получают щедрые бонусы на более выгодных условиях.
Другие виды бонусов, которые могут получить игроки: промокоды, кэшбэк, бездепозиты, релоады, персональные подарки. Казино регулярно проводит акции и турниры с крупным призовым фондом. Каждый игрок может выиграть миллионный джекпот, сделав минимальную ставку.
Техподдержка
Самый простой способ получить помощь — написать в чат.
- Владелец: Не указана
- Live Chat: Да
- E-mail: support@vegas-grand.info
В этом казино есть все, что нужно для игры: разнообразные игры, бонусы и турниры. Одно из главных преимуществ — это предоставление бонуса при регистрации, который можно использовать для игры на игровых автоматах.
Я считаю, что это казино довольно хорошее — здесь много игровых автоматов, сайт работает быстро, а техническая поддержка всегда готова помочь. В последнее время мне очень везет, и я выигрываю много денег, что, конечно, очень приятно. Я буду продолжать играть и надеяться на удачу.
Я недавно начал играть в казино Vegas Grand и уже получил хорошие результаты. У меня были отличные выигрыши, а также я оценил хорошую бонусную программу для новичков и быстрый вывод денег.